How to Remove a Hidden Virus from an Infected Flash Drive Without an Antivirus Program

Removing virus from an external device without using an antivirus software
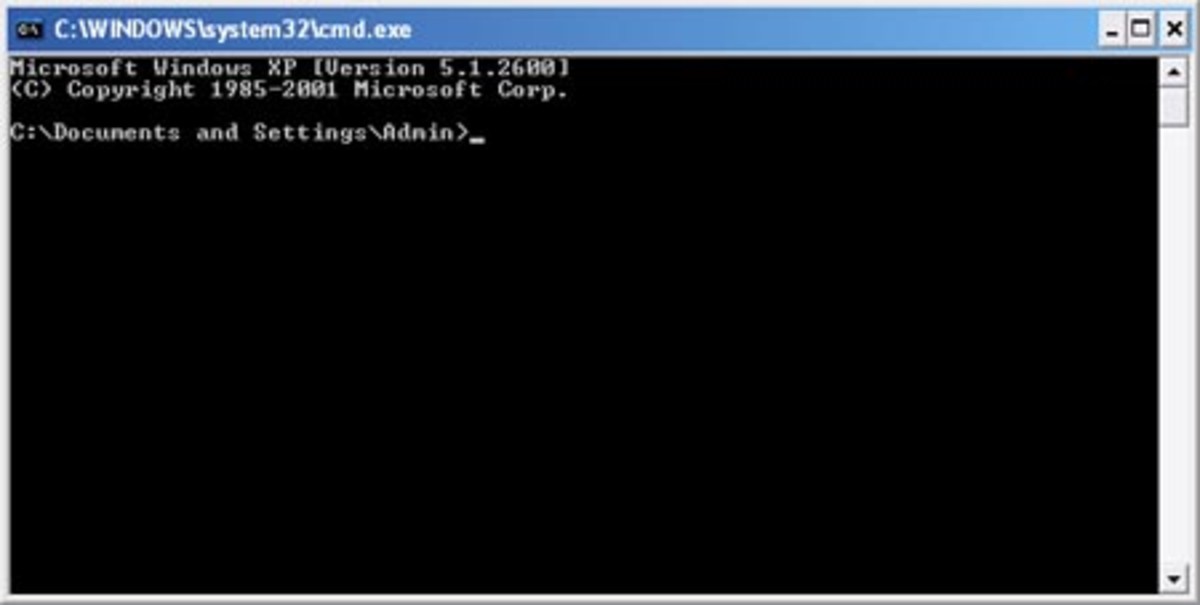
There are many good antivirus programs out there but in case you don’t want to use one, or you suspect that the one you have is not detecting the virus or maybe you are using someone else’s computer and want to do a quick check, you can do these simple steps to check and clean the external device. This method uses the Command Prompt program in Windows operating systems. Command Prompt used to be the Disk Operating System or DOS – the one that came before Windows.
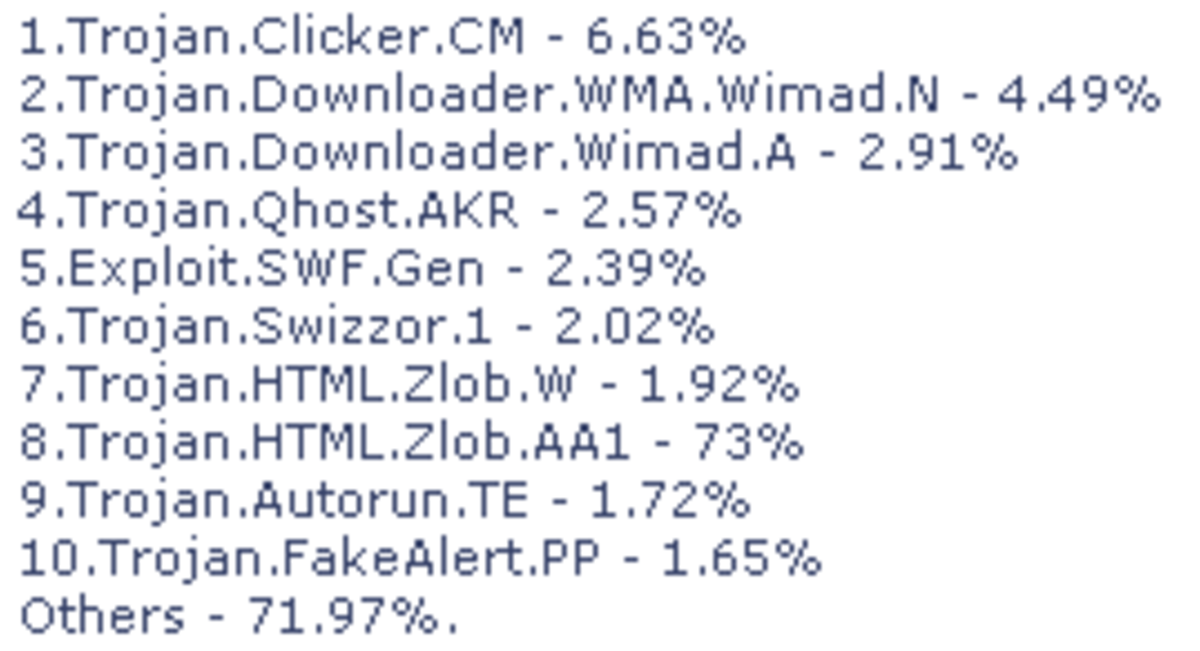
Before we start, you need to know some of the behaviors and characteristics of some viral files. First, they hide themselves. They take on the System, Hidden and Read-only attributes. Next, in order to spread, they need to be automatically run. Expect an autorun.inf file that is hidden in the root directory of your storage device or flash drive (sometimes this happens too in Optical drives or CDs). And sometimes they hide themselves in a folder and make the folder hidden. Other viruses also change your folders to *.exe files so you get to run them yourself. So you need to look for these signs when checking for viruses.
Assume that you have a flash drive which took F: for its drive letter. To check that drive, Click start, then type “cmd” then enter. This opens Command Prompt. Windows XP users need to type “run” then enter after clicking start. Once you are in the Command Prompt interface type these:
F:
Attrib
What that does is list all files and their attributes in the root directory. Look for the ones mentioned above then once you have identified them you can proceed to changing their attributes using the attrib command. Type “attrib –s –h –r” then hit enter. This removes the system, hidden and read-only attributes of all files in the root directory. Now you can delete them. Type these:
Del autorun.inf
Del filename.exe
This command deletes the autorun.inf file and the virus. Filename is the filename of the .exe file that had a System, Hidden and Read-only or SHR attribute. If there is more than one add more lines. If you have those .exe files masquerading as folders, do the del command for each of the .exe file or just type “del *.exe” which deletes all .exe files in the root directory.
To check for hidden folders, type “attrib /s /d” – same as the one above but it also lists the directories or folders. the “/s /d” are switches which tells the attrib command to include all folders and subdirectories. To remove or delete a folder type “rmdir foldername /s /q” – foldername is the name of the SHR folder. There is no need to remove the attribute before you can erase it.
However, after doing any of the steps and what you have done is reverted, the virus may be running in the system. Example is when you delete autorun.inf then it comes back or if you change the attributes and it goes back to SHR. In this it is better to get a virus removal tool to do the job. It will be easier. So, when opening a flash drive or any external device you suspect to have a virus, do not just double click on it in My computer. Instead, right click then select the explore option or you can just go directly to command prompt then look for the viruses.